Use a VPN on Your Work Computer: The Dos, Don'ts, and Why It Matters
Use a vpn on your work computer the dos donts and why it matters. Quick fact: using a VPN on a work device can protect your data, but it can also violate company policy if misused. This guide breaks down practical steps, best practices, and potential pitfalls so you can stay safe and compliant. Below is a fast-start guide, then a deeper dive with tips, real-world examples, and checklists.
- What you’ll learn:
- When to use a VPN on a work computer
- The dos and don’ts to avoid policy breaches and security risks
- How VPNs affect performance, logging, and access
- How to choose a VPN that fits a corporate environment
- Common mistakes and how to fix them
Useful resources and quick links text only Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, VPN basics - en.wikipedia.org/wiki/Virtual_private_network, Cybersecurity and your work device - cisa.gov, Tech policy guides - thinkgoogle or your company intranet
Why a VPN on a Work Computer Matters
- Security in transit: A VPN encrypts traffic between your device and the VPN server, shielding sensitive data from prying eyes on public or shared networks.
- Remote work resilience: When you’re on the road or at a coffee shop, a VPN helps you maintain a private channel to your corporate network.
- Access management: Some apps and internal tools require VPN access to reach corporate resources.
- Compliance and policy: Many organizations mandate VPN use for protecting customer data and sensitive information.
However, there are important caveats. A VPN can mask activity, complicate troubleshooting for IT, and violate policies if used to bypass controls. The goal isn’t to hide from security teams but to create a secure, compliant workflow.
Dos: Smart, Safe Practices
Do: Check your company policy first
- Read the official VPN and remote-access policy.
- Confirm approved vendors, configurations, and any monitoring expectations.
- If in doubt, ask IT before enabling a VPN on your work device.
Do: Use a company-approved VPN client
- Stick with the vendor sanctioned by IT e.g., the one they’ve tested and approved.
- Ensure you’re using the latest version to avoid known vulnerabilities.
Do: Enable multi-factor authentication MFA
- MFA adds a second layer of protection beyond passwords.
- It’s often required for VPN access to reduce the risk of credential theft.
Do: Keep devices compliant and updated
- Install OS and security updates promptly.
- Maintain current antivirus/EDR solutions.
- Ensure disk encryption is enabled FileVault on macOS, BitLocker on Windows.
Do: Only access work resources through the VPN
- Use the VPN for internal sites, databases, and file shares.
- Avoid personal browsing or non-work apps that route traffic through VPN if policy prohibits it.
Do: Use split-tunneling only if approved
- Split tunneling lets only some traffic go through the VPN, reducing load and latency.
- Many orgs disallow it due to security concerns; follow policy.
Do: Monitor performance and report issues
- If VPN slows down productivity, flag it to IT with details time, app, bandwidth usage.
- Report any unexpected disconnects or certificate errors immediately.
Do: Practice good password hygiene and device hygiene
- Use unique passwords, rotate them per policy, and store them in a secure manager.
- Lock your device when you step away, and don’t leave it unattended.
Do: Log out when not in use
- Terminate VPN sessions when not actively working on corporate resources.
- Don’t leave sessions open on shared machines.
Do: Back up critical work
- Ensure work is saved to corporate cloud or approved repositories.
- Avoid saving sensitive work locally where it could be at risk.
Don’ts: Common Pitfalls to Avoid
Don’t bypass IT controls
- Don’t install unapproved proxies, add-ons, or alternate VPNs.
- Don’t disable firewalls or security software to force a cleaner connection.
Don’t use personal devices or personal VPNs for work tasks
- Mixing personal VPNs with corporate networks can leak data or introduce risks.
- Follow policy about device boundaries and the approved setup.
Don’t share VPN credentials
- Treat VPN login details like a master key.
- Don’t post them in chat apps, shared docs, or email threads.
Don’t route non-work traffic through the VPN unless allowed
- Personal streaming, gaming, or non-work apps can cause unnecessary load and could breach policy if allowed.
Don’t ignore malware or phishing signs
- VPNs don’t replace good security hygiene.
- If you suspect phishing or malware, isolate the device and notify IT.
Don’t ignore performance issues
- If you notice consistent latency, packet loss, or disconnects, don’t shrug it off.
- IT may need to push a configuration change or upgrade VPN hardware.
Don’t forget about data sovereignty and logging
- Some VPNs log activity; understand what data is collected and who can access it.
- Ensure you’re comfortable with the privacy implications of the VPN you’re using.
Don’t assume “VPN equals invincible”
- A VPN doesn’t make you invulnerable to phishing, social engineering, or insecure endpoints.
- Combine VPN with good security practices, like not clicking suspicious links.
Don’t ignore the impact on collaboration tools
- Some VPNs can interfere with VoIP, conferencing, or real-time collaboration apps.
- If you notice стабильный drop in audio/video quality, work with IT to adjust routes or firewall rules.
Don’t neglect backup plans
- Have a fallback plan if VPN access is temporarily unavailable.
- Know who to contact and how to access critical systems during outages.
How VPNs Interact with Company Networks
- Access control: VPNs often enforce role-based access, ensuring only authorized users reach sensitive resources.
- Network segmentation: VPN routes can keep sensitive segments isolated from the broader internet.
- Logging and auditing: IT teams use VPN logs to trace access and investigate incidents.
- Compliance alignment: Some industries require strict VPN use to protect personal data e.g., healthcare, finance.
Pro tip: If you’re frequently working remotely, ask IT about a fixed IP or a more predictable routing pattern. It can stabilize performance and reduce authentication friction.
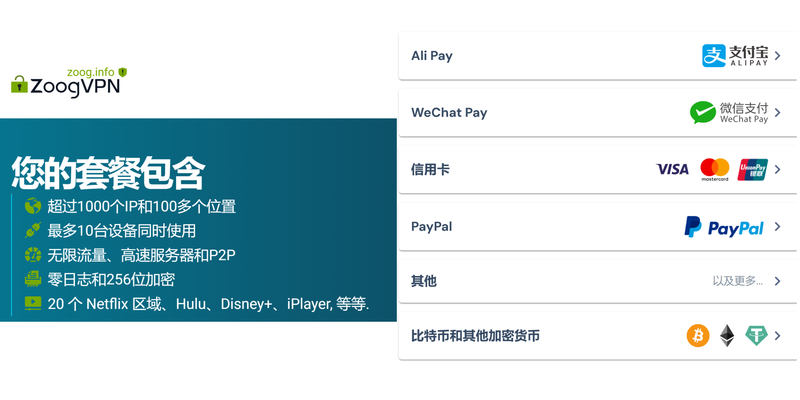
How to Choose a VPN for Work
- Approval and policy compatibility: Confirm the VPN solution is approved and compatible with enterprise security standards.
- Security features: Look for strong encryption AES-256, robust authentication MFA, certificate-based, and leak protection.
- Privacy posture: Understand the VPN’s logging policy and data retention practices.
- Compatibility and management: Ensure it works across your devices and integrates with your company’s identity provider e.g., SSO, AD, Okta.
- Performance considerations: Seek solutions with reliable throughput and minimal latency for your typical workload.
- Support and onboarding: A vendor with solid IT support and clear deployment guides helps your team avoid misconfigurations.
- Compliance certifications: Check for ISO 27001, SOC 2, and other relevant certifications.
Real-World Scenarios and Examples
Scenario 1: Remote onboarding
- You’re at a cafe and need to access HR software. You connect to the company VPN, MFA prompts appear, you log in, and you’re granted access to the internal resources necessary for onboarding. You log out when done and monitor for any unusual prompts.
Scenario 2: Domestic travel
- On a flight with limited connectivity, you still need to review sensitive documents. The VPN keeps your data encrypted, but you should limit bandwidth-heavy tasks if the connection is unstable.
Scenario 3: Security incident response Unlock secure internet anywhere your complete guide to fastvpn tethering
- IT detects suspicious login attempts. You’re asked to disconnected and re-authenticate. You follow the steps, provide log details, and wait for IT’s guidance.
Performance and Security Best Practices
- Optimize your home office setup for VPN performance:
- Use a wired connection when possible to reduce latency.
- Place your router in a central location and minimize interference from other devices.
- Security hygiene:
- Enable automatic updates for your OS and VPN client.
- Use a reputable VPN provider with strong encryption and a solid no-logging policy or clear logging policies.
- Data safety:
- Avoid sharing credentials, especially in chat apps or docs.
- Regularly review access rights and revoke unused accounts.
SEO-Rich Tips and Metadata
- Target keywords: Use a vpn on your work computer the dos donts and why it matters, VPN on work computer guidelines, corporate VPN best practices, remote work VPN policy.
- Use long-tail variants naturally: “how to use vpn on work laptop safely,” “do’s and donts of corporate VPN use,” “VPN performance tips for remote work.”
- Include structured data and FAQs to boost snippet potential.
Tools and Resources for Further Reading
- NIST guidelines on VPN security and remote access
- CIS Controls for endpoint protection
- Vendor-specific deployment guides for popular VPN clients
- Company IT policy documents and security awareness training modules
- Industry compliance frameworks relevant to your sector
Frequently Asked Questions
How does a VPN protect data on a work computer?
A VPN encrypts traffic between your device and the corporate network, preventing eavesdropping on unsecured networks and helping protect sensitive information from interception.
Should I always use a VPN on my work computer?
Not always. Use it when connecting to internal resources, handling sensitive data, or working from public networks, and only if your policy requires it.
Can a VPN slow down my internet connection?
Yes, VPNs can introduce latency due to encryption and routing. If you experience slowdowns, check with IT for optimized settings or alternatives.
What is split tunneling, and should I use it?
Split tunneling sends some traffic over the VPN and some directly to the internet. It can improve performance but may violate policy or reduce security, so follow your IT guidance.
How do I know which VPN client to install?
Use the VPN client approved by your employer. If in doubt, ask IT for the exact client to install. Soundcloud not working with vpn heres how to fix it fast — Quick Fixes, Pro Tips, and VPN Tricks to Unblock SoundCloud Now
Is MFA required for VPN access?
Many organizations require MFA for VPN access to add a second factor of authentication.
Can VPNs leak my data outside the corporate network?
If configured correctly, VPNs protect data in transit. However, DNS leaks or misconfigurations can expose some traffic; follow IT’s setup guidelines to prevent leaks.
What should I do if the VPN disconnects?
Document the issue and contact IT. Avoid continuing work on sensitive tasks if the connection is unstable.
Are there privacy concerns with corporate VPNs?
VPNs may log connection metadata and usage. Review the policy to understand what data is collected and who can access it.
How can I optimize VPN performance for video calls?
Prioritize a stable connection, consider disabling bandwidth-heavy apps, and ensure QoS settings are aligned with your IT team’s recommendations. Krnl Not Working With Your VPN Here’s How To Fix It: VPN Troubleshooting, Latency, and Safe Bypass Techniques
Sources:
Why your vpn keeps turning on and how to fix it
免费vpn推荐:最值得信赖的免费与低成本VPN選擇與實用指南
Why your vpn isnt working with mobile data and how to fix it 2026
Mullvad vpn what reddit really thinks and why it matters
Ios翻墙v2ray:實用指南與最新 Trend,搭配 V2Ray 設定與 VPN 比較 How to set up an OpenVPN server on your Ubiquiti EdgeRouter for secure remote access