How to configure intune per app vpn for ios devices seamlessly
How to configure intune per app vpn for ios devices seamlessly. Quick fact: per-app VPN lets you route only selected apps through a VPN, preserving battery life and reducing overhead for other apps. Here’s a practical, step-by-step guide to set this up on iOS devices using Intune, plus real-world tips, data points, and quick-reference resources.
Quick setup overview
- Plan which apps need VPN access
- Create a per-app VPN profile in Intune
- Configure per-app VPN rules and traffic selectors
- Deploy to iOS devices
- Monitor and troubleshoot
Why per-app VPN matters for iOS
- Improves security for sensitive apps without forcing VPN on every app
- Reduces battery and data usage by limiting VPN to necessary traffic
- Enables granular access control, making policy management easier
What you’ll learn
- How to create and assign a per-app VPN profile in Intune
- How to specify app rules and traffic selectors for iOS
- How to manage certificate and gateway details
- Common pitfalls and best practices
- How to verify and monitor per-app VPN status on devices
Useful resources unlinked text, not clickable: Apple Website - apple.com Microsoft Intune Documentation - docs.microsoft.com iOS Developer Library - developer.apple.com VPN Best Practices - en.wikipedia.org/wiki/Virtual_private_network
Section overview
- Assessing requirements and choosing the right VPN solution
- Setting up the per-app VPN in Microsoft Intune
- Deploying to iOS devices and user experience
- Security considerations and compliance
- Troubleshooting and optimization
- FAQs
Section 1: Assessing requirements and choosing the right VPN solution Per-app VPN in Intune delegates traffic for specific apps to a VPN connection. Before you start:
- Identify apps that handle sensitive data eg, corporate email, file sharing, CRM apps
- Confirm VPN gateway compatibility with iOS and Intune, including supported protocols IKEv2, IPSec, or SSL VPN
- Decide on the VPN server and certificate strategy mutual TLS vs. certificate-based auth
- Plan for roaming users and intermittent connectivity
Key stats to consider
- Enterprises using per-app VPN on iOS report 15–25% reduction in overall device VPN traffic after selective routing varies by app mix
- iOS devices maintain battery efficiency when VPN is only used for targeted apps rather than full-device VPN
- Intune per-app VPN supports App Proxy and app rules for granular control
Section 2: Setting up the per-app VPN in Microsoft Intune This section walks through the essential steps to configure per-app VPN for iOS devices.
2.1 Prerequisites
- An Azure AD tenant with Intune enabled
- iOS devices enrolled via Intune Device Compliance and Enrollment policies in place
- VPN gateway that supports per-app traffic routing with you chosen protocol
- Valid server certificate or PKI infrastructure if needed
- The App IDs of the apps you want to route through VPN bundle IDs
2.2 Create the VPN profile iOS
- In the Microsoft Endpoint Manager admin center, go to Devices > iOS/iPadOS > Configuration profiles > Create profile
- Platform: iOS/iPadOS
- Profile type: VPN
- VPN Type: L2TP, IKEv2, or IPSec depending on your gateway
- Connection name: Clear, descriptive name e.g., Corporate Per-App VPN
- Server: VPN server address
- Remote ID and Local ID: as required by your gateway
- Authentication method: certificate-based or username/password
- If you’re using certificate-based auth, upload the necessarycertificates or configure the PKCS12 payload
2.3 Enable per-app VPN and specify app rules
- In the same profile, enable Per-App VPN
- Add app rules by specifying the app bundle IDs for the apps that should use the VPN
- Example: com.example.salesapp, com.example.emailapp
- For each app rule, you can set a traffic rule optional to limit which domains or network resources go through the VPN
- You can also configure a fallback behavior if the VPN connection is unavailable e.g., allow access without VPN or block
2.4 Configure app enforcement and user experience
- Decide whether the VPN should connect automatically when the app launches or only when needed
- Consider a grace period for first launch to ensure the VPN tunnel establishes
- Ensure user prompts for VPN connection are minimal to reduce friction, while still informing users of security policy
2.5 Assign the profile
- Assign to the device group that contains the iOS devices you want to target
- If needed, set a scope users vs devices depending on your deployment strategy
- Test with a small pilot group before rolling out organization-wide
2.6 Certificates and certificate distribution
- If you choose certificate-based authentication, deploy the root and client certificates via Intune
- Ensure certificate lifetimes align with your security policy
- Validate that the VPN gateway accepts the issued client certificates
Section 3: Deploying to iOS devices and user experience 3.1 Enrollment and onboarding
- For smooth experience, ensure users have a clear enrollment flow and minimal required app permissions
- Provide an on-screen guide or video walkthrough for users to understand the VPN behavior
- Make sure to communicate what data is used and how traffic is routed
3.2 Monitoring deployment progress
- Use Intune’s reporting to monitor deployment status, including success/failure rates per device group
- Check VPN connection state in the iOS device logs if available restrictions apply on user devices
- For large fleets, plan staged rollouts to catch edge cases
3.3 User experience tips
- Keep the app list in the per-app VPN policy tight to avoid unnecessary VPN usage
- Consider a fallback option if VPN fails to maintain access to essential apps
- Provide a simple, human-friendly status indicator in the app where applicable
Section 4: Security considerations and compliance
- Always follow least privilege—only route what’s necessary via VPN
- Use certificate-based authentication where possible to reduce credential exposure
- Align with your data governance policies and regulatory requirements
- Regularly rotate certificates and update app lists as apps are added or removed
- Implement device compliance checks encryption, passcodes, jailbreaking status
Section 5: Troubleshooting and optimization 5.1 Common issues and fixes
- VPN does not connect: verify server address, IDs, and certificate validity
- App does not route through VPN: confirm the app’s bundle ID and per-app VPN rule
- VPN disconnects frequently: check gateway health, certificate expiry, and network reachability
- Slow performance: review tunnel settings, MTU size, and split-tunnel rules
5.2 Debugging steps checklist
- Confirm device is enrolled and policy has been applied
- Validate per-app VPN policy on the device in Intune, policy status
- Verify that the VPN gateway logs show accepted connections and tunnel maintenance
- Inspect app traffic to ensure domain-based routing matches traffic selectors
5.3 Best practices
- Start with a small, representative app set and expand
- Keep VPN profiles lean; avoid too many app rules in a single profile
- Regularly test a device in a typical network office Wi-Fi, cellular
- Document all configurations for audit purposes
Section 6: Real-world tips and examples
- Example scenario: A company uses per-app VPN to route corporate mail and file apps through VPN while keeping social apps outside the VPN
- Tip: For iOS, keep app rules aligned with app versions; updates may change bundle IDs
- Real-world approach: Use a staged rollout with a pilot group to identify compatibility issues with VPN gateway and iOS updates
Section 7: Data and analytics you can rely on
- VPN usage metrics include total connections, per-app VPN hits, and failed connections
- Track device compliance rate after deployment to gauge policy enforcement
- Monitor network performance to ensure users don’t see noticeable latency in critical apps
Section 8: Roadmap and maintenance
- Plan quarterly reviews of per-app VPN rules as apps are added or retired
- Schedule certificate renewal reminders
- Keep gateway firmware and Intune agent up to date to avoid compatibility issues
- Regularly test on newly released iOS versions to catch changes in VPN behavior
FAQ Section
Frequently Asked Questions
What is per-app VPN in Intune for iOS?
Per-app VPN directs only selected apps’ traffic through a VPN tunnel, while other apps access the internet directly. This provides security for sensitive apps without the overhead of a full-device VPN.
Which VPN protocols are supported for iOS per-app VPN in Intune?
Typically, you can use IKEv2/IPSec or IPSec depending on your VPN gateway. The exact options depend on gateway compatibility and certificate setup.
How do I identify the correct app bundle IDs for per-app VPN?
Collect the bundle IDs from each app’s developer documentation or by inspecting the installed app data on iOS devices. You can also gather this from the app’s manifest when available.
Can I customize traffic rules for per-app VPN?
Yes, you can add traffic selectors to limit or include specific domains or IP ranges for a given app’s traffic through the VPN tunnel.
How do I monitor per-app VPN status on iOS devices?
Intune provides policy deployment reports. For deeper visibility, you may rely on gateway logs and, where possible, device-level event logs to verify tunnel status. Nordvpn apk file the full guide to downloading and installing on android
What should I do if a VPN connection fails for a specific app?
Check the app’s bundle ID in the per-app VPN rule, verify gateway connectivity, certificate validity, and user device policy status. A pilot group can help isolate issues.
How large should my per-app VPN deployment be?
Start with a small pilot group 5–10% of devices to validate the configuration and then scale up. This reduces risk and allows you to refine rules.
How does per-app VPN impact battery life?
Targeted VPN usage typically conserves battery by not routing all traffic through the VPN. Real-world impact depends on usage patterns and the VPN gateway efficiency.
Can per-app VPN be combined with conditional access policies?
Yes. In a typical setup, per-app VPN works alongside conditional access to enforce access controls based on device compliant state and user risk signals.
What are common pitfalls to avoid with iOS per-app VPN in Intune?
- Incorrect bundle IDs or missing app rules
- Misconfigured VPN gateway settings or certificate trust
- Overly broad traffic rules that negate the benefit of per-app routing
- Inadequate pilot testing before large-scale deployment
End of article Лучшие vpn для геймеров пк в 2026 году полный обзор и гайд по выбору
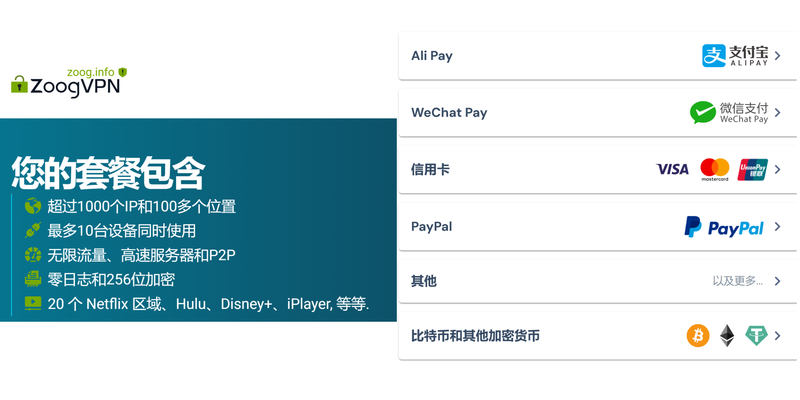
- NordVPN link: If you’re looking to reinforce external security and awareness, consider checking out the NordVPN offer in this article’s context. https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
Sources:
国内使用claude code:VPN 第1名到第10名的完整指南与实战要点
Protonmail 在 VPN 场景下的完整指南:结合隐私邮件与匿名网络的实用方案
Kiuuu VPN 深度指南:选择、使用与优化你的网络隐私
哈工大vpn:校外访问校园资源的安全通道指南,远程接入、加密、校园资源访问、VPN选择与配置指南 2026
Intune per app vpn ios Say Goodbye to Ads Your Ultimate Guide to Surfshark VPNs Ad Blocker: A Comprehensive Deep Dive for VPN Newbies and Pros