Scamoreal Home Overview
Welcome to Scamoreal
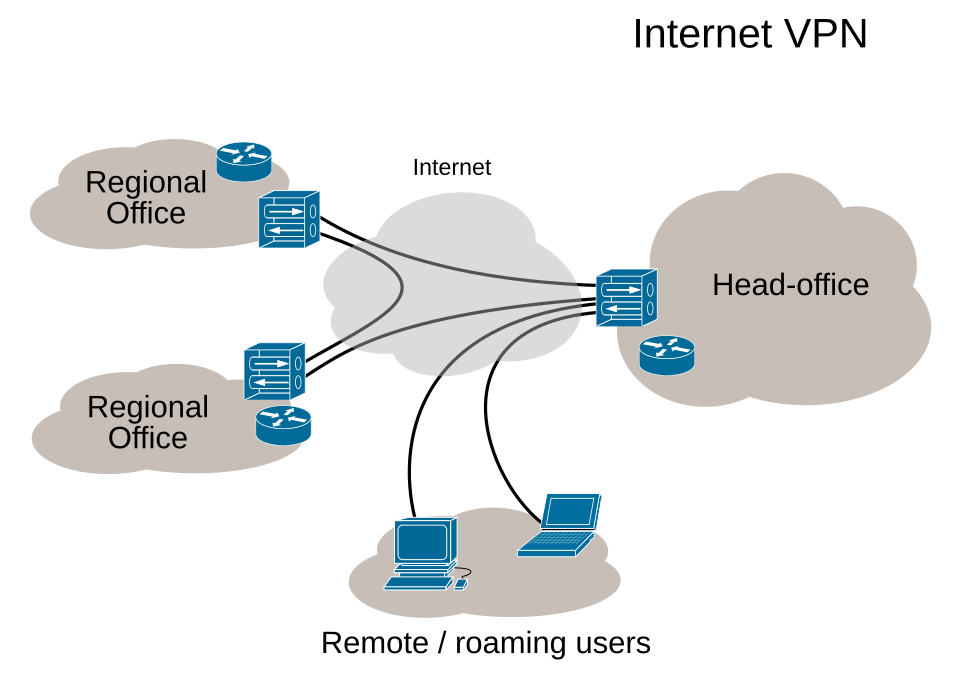
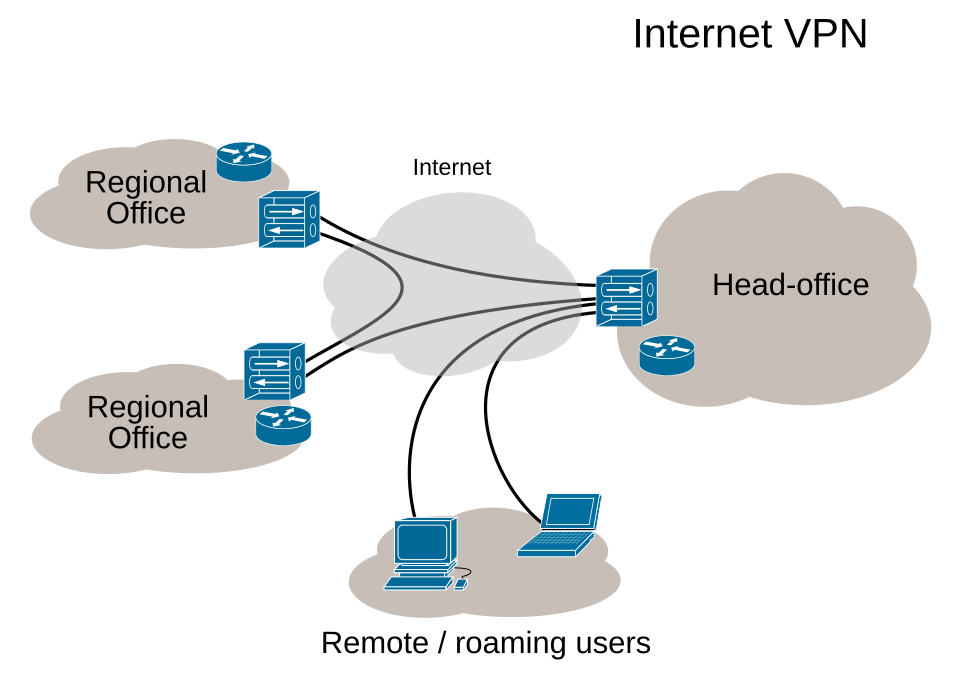
We provide honest comparisons and side-by-side picks for readers who want clear, practical guidance on VPNs, privacy tools, and streaming access. This home section serves as an orientation to how we evaluate services, what matters most to everyday users, and how to read our tests. Our coverage combines hands-on testing, policy notes, and price clarity to help you decide with confidence.
What you’ll find here includes practical guidance on setup and use, real-world performance checks, and transparent looks at pricing and features. In this orientation, we touch on key topic clusters: privacy and security basics, performance and compatibility across devices, streaming and geo-access, pricing and value, and policy and regulator context. We also highlight how to compare providers side by side, with clear takeaways you can apply to your own decision-making.
What we measure matters. We compare providers by account structure, features, and restrictions that influence daily use. Expect analysis of kill switches, DNS leakage protection, split tunneling, platform support, simultaneous connections, and customer support responsiveness. We also note regulatory environments that affect privacy choices in broad terms, without tying our observations to any single country or region.
Scamoreal’s stance is grounded in transparent, practical evaluation. We avoid hype and focus on what works for real users: reliable access to content, predictable performance, straightforward pricing, and clear user guidelines. Our goal is to help you choose products that balance privacy, speed, and value, while avoiding gimmicks that overstate capability or underdeliver on basic protections.
How we present information is designed for fast decision-making. Expect concise summaries, side-by-side comparisons, and numerical details where they matter. We translate technical terms into plain language and show how different features influence everyday tasks like streaming, file sharing, and remote work. When relevant, we provide local-context references that readers in the United States and abroad can recognize, without assuming a specific locale beyond general international use.
Top clusters you’ll encounter in this space include:
- Privacy basics: encryption standards, zero-logging claims, jurisdiction considerations, and data protection practices from major providers like NordVPN and ExpressVPN.
- Performance and compatibility: speed, latency, compatibility across Windows, macOS, iOS, Android, and routers; considerations for streaming devices and smart TVs.
- Streaming and geo-access: circumventing regional restrictions, platform-specific limitations, and common workarounds for Prime Video, Hotstar, and other services.
- Pricing and value: monthly versus annual plans, discount cycles, refund policies, and added-value features such as ad blocking or malware protection.
- Policy and regulation: how privacy laws and data retention expectations shape user choice, with notes on global and regional trends without anchoring to a single country.
- Practical setup tips: common installation steps, browser extensions, and troubleshooting for startup and background processes that affect everyday use.
Country-specific context we reference aims to reflect a broad international audience while grounding examples in familiar, non-region-specific scenarios. For instance, we discuss standard price presentation and payment options that typically appear in USD on many global platforms, as well as common device ecosystems and streaming services that are widely recognized across markets. This approach keeps content relevant to readers in the United States and abroad, including references to typical local payment methods and consumer protection expectations without tying the analysis to any single jurisdiction.
What to expect from our home page is a curated view that orients new readers and assists returning ones in quickly orienting to the current landscape. You’ll see upcoming feature notes, quick-start guidance, and a clear path to deeper reviews and practical how-tos. The home page is designed to be a launching point for deeper dives into topics like setup optimization for Edge, Windows, macOS, Android, and iOS, as well as strategic comparisons among popular providers.
Pricing and plans you’ll see discussed emphasize clarity. For example, we compare standard and premium tiers, explain what features are included at each level, and identify typical price points in USD. When we reference specific services such as NordVPN or ExpressVPN, we distinguish between basic protections, specialized servers, and add-on features like threat protection or split tunneling, so you can decide which combination best fits your needs.
How to use this home page is straightforward. Scan the overview to identify your priority—whether it’s accessing streaming libraries, securing public Wi-Fi, or maintaining privacy while browsing. From there, navigate to the linked top posts to see in-depth analyses of current topics like VPN compatibility with Microsoft Edge, and common issues such as startup background processes. This orientation exists to help you move efficiently from curiosity to a well-informed choice.
One more note on tone and approach: we keep language precise and practical, avoiding overused or sensational phrasing. You’ll see clear data points, concrete examples, and a focus on what actually affects day-to-day use. The aim is to empower you with a reliable, neutral lens for evaluating tools that affect privacy, streaming access, and overall online security.
What to expect in the upcoming sections
As you explore further, you’ll encounter side-by-side reviews and data-driven comparisons that cover:
- Security features such as encryption standards, kill switches, and DNS protection, with notes on platform differences.
- Performance metrics including speeds, ping, and consistency across servers in multiple regions.
- Streaming compatibility with popular platforms and known blockers, including frequently reported services like Prime Video and Hotstar.
- Value considerations focusing on price per month, yearly commitments, and included perks.
We acknowledge the dynamic nature of the market. Availability, pricing, and features change over time, so the home page offers a framework for navigating updates and new entries with a steady, principled approach.
Illustrative table: quick service and plan snapshot
| Provider | Plan | Price (USD) | Key features |
|---|---|---|---|
| NordVPN | Standard | 11.99 | No-logs policy, Kill Switch, 6 devices |
| ExpressVPN | Monthly | 12.99 | Broad device support, Split tunneling |
| Scamoreal Favorites | Annual | 8.99 | Privacy-centric features, user-friendly |
Note: all prices shown are in USD and subject to change. Local taxes and promotions may apply.
Recent in other languages
Latest posts across 17 languages